Organizations today depend heavily on digital systems to manage data, communication, and business operations. As cyber threats continue to increase, companies must implement structured security frameworks to protect sensitive information and maintain trust. Because of this growing demand for security professionals, many learners begin their journey with an Information Security Management Course to understand how organizations manage and protect information assets.
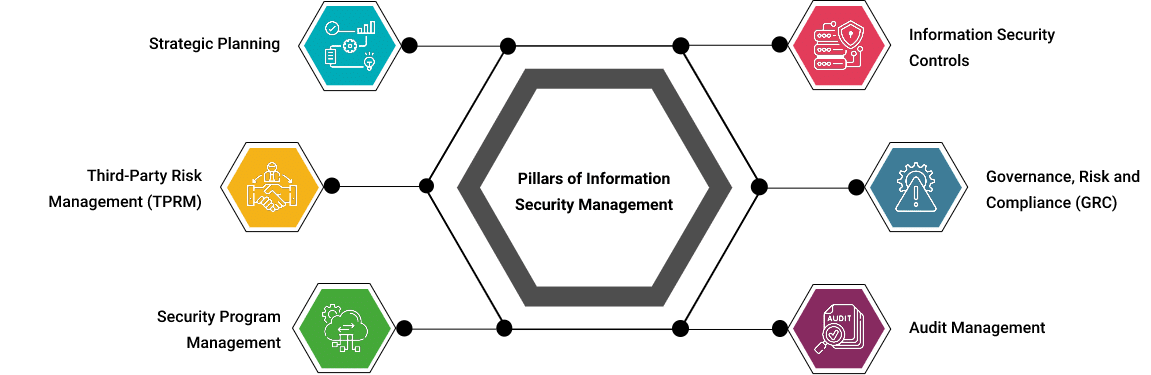
An information security management system is a structured framework that organizations use to protect sensitive data and ensure that security processes are properly managed. These frameworks include policies, procedures, technologies, and risk management strategies designed to maintain the confidentiality, integrity, and availability of information.
Many beginners explore these concepts through an information security management system training course, which introduces the principles of security governance, compliance standards, and risk management processes. Information Security Management Course type of training helps learners understand how organizations develop security strategies and implement structured protection mechanisms.
As cybersecurity becomes a priority for businesses across industries, professionals are increasingly enrolling in specialized programs such as an information systems security manager course to develop the skills needed to manage enterprise security programs. These courses help learners understand how security policies are designed, implemented, and monitored within large organizations.
Another important aspect of security management is risk analysis. Through an information security risk management course, students learn how organizations identify threats, analyze vulnerabilities, and implement strategies to reduce potential risks. Understanding these risk management principles is essential for maintaining strong security practices in modern digital environments.

Why an Information Security Management Course Is Important for Modern Organizations
Modern organizations handle large amounts of sensitive information, including financial records, customer data, and internal business documents. Without effective protection mechanisms, this information can become vulnerable to cyberattacks, data breaches, and unauthorized access.
Implementing strong information security management systems allows organizations to create a structured approach for protecting their information assets. These systems provide clear guidelines for identifying security risks, implementing protective controls, and continuously monitoring system security.
Security management frameworks also help organizations comply with industry regulations and security standards. Many industries must follow strict data protection laws that require organizations to implement structured security practices. An information security management system training course often introduces learners to these regulatory requirements and explains how organizations align their security policies with global security standards.
Companies are increasingly seeking professionals who understand how to manage security programs and ensure compliance with security frameworks. This demand has made training programs such as the information systems security manager course valuable for individuals who want to pursue careers in cybersecurity management and information security leadership.
Step-by-Step Process to Learn Through an Information Security Management Course
Understanding security management concepts becomes easier when learners follow a structured learning path. Most professional programs organize their curriculum in stages so students can gradually build their knowledge.
Step 1: Information Security Fundamentals in an Information Security Management Course
The first step in an Information Security Management Course focuses on learning the core principles of information security. Students learn about confidentiality, integrity, and availability, which form the foundation of protecting digital information.
At this stage, learners also explore how an information security management system is designed to protect organizational data and support secure business operations.
Step 2: Risk Assessment Skills in an Information Security Management Course
After understanding the fundamentals, students begin studying risk assessment processes. Topics from an information security risk management course help learners understand how organizations evaluate security threats and identify vulnerabilities.
Students also learn how security policies and procedures guide employees and administrators in maintaining secure systems and protecting sensitive data.
Step 3: Managing Security Systems in an Information Security Management Course
The final stage focuses on managing enterprise security frameworks and monitoring security performance. This stage often overlaps with training provided in an information systems security manager course, where learners develop both technical knowledge and leadership skills required to manage organizational security programs.
Expert Insights on Information Security Management
Security professionals often explain that effective cybersecurity is not only about installing security tools. It also involves governance, policies, and structured management processes. Experts working in enterprise cybersecurity environments emphasize that organizations must implement strong information security management systems to maintain consistent protection of their digital assets.
According to experienced security managers, one of the most important parts of cybersecurity management is risk assessment. Organizations must first identify possible threats before implementing security controls. Training programs such as an information security risk management course help learners understand how to evaluate vulnerabilities, assess potential risks, and create strategies that reduce security threats.
Another insight shared by professionals is the importance of leadership in information security management. Security managers must coordinate with different departments, develop security policies, and ensure that all teams follow proper security procedures. This is why many professionals enroll in an information systems security manager course to develop both technical knowledge and management skills required to lead security initiatives.
Experts also highlight that information security is a continuous process. Organizations regularly review their information security management system to identify weaknesses, update security policies, and respond to new cyber threats that appear in the digital landscape.
Tools and Resources for Learning Information Security Management
Learning cybersecurity management becomes easier when learners use structured training resources and practical tools. Many training programs provide case studies, security frameworks, and risk assessment exercises to help students understand how organizations implement security programs.
Security documentation templates are commonly used learning resources. These templates help students understand how to document security policies, risk registers, and compliance reports within an organization.
Another useful learning method is studying real-world security frameworks that organizations use to protect their information assets. A structured information security management system training course often introduces learners to these frameworks and demonstrates how they are implemented in enterprise environments.
If you want to build strong knowledge of cybersecurity governance and understand how organizations implement structured security frameworks, you can explore this training program: click here
This course helps learners understand information security management systems, develop risk management skills, and learn how organizations design and manage security policies to protect sensitive information.
Common Mistakes Beginners Make While Learning Information Security Management
Many beginners encounter similar challenges when they start learning about information security management. Recognizing these mistakes early can help learners improve their understanding of cybersecurity frameworks.
One common mistake is focusing only on technical security tools. While technical tools are important, effective cybersecurity also requires strong governance and policy management. An Information Security Management Course teaches learners how policies, procedures, and risk management strategies work together to protect information.
Another mistake is ignoring risk assessment processes. Without understanding risk management principles, it becomes difficult to design effective security controls. Topics covered in an information security risk management course help learners understand how organizations identify threats and develop risk mitigation strategies.
Some learners also underestimate the importance of documentation. Security policies, compliance reports, and risk assessment documents are critical components of a well-managed information security management system.
Finally, beginners sometimes try to learn everything at once. A structured information security management system training course helps learners build knowledge gradually and understand complex security concepts step by step.
Frequently Asked Questions About Information Security Management Course
Q1: What is an Information Security Management Course?
An Information Security Management Course teaches professionals how organizations protect sensitive data using structured security frameworks, policies, and risk management processes.
Q2: Who should take an information security management course?
Information Security Management Course IT professionals, cybersecurity learners, system administrators, and security analysts can benefit from learning about information security management systems and security governance practices.
Q3: What skills will I learn in this course?
Students learn risk assessment methods, security policy development, compliance management, and strategies used to implement effective information security management systems.
Q4: Is information security management important for cybersecurity careers?
Information Security Management Course Yes. Understanding information security management systems is important for professionals who want to work in cybersecurity governance, compliance management, or security leadership roles.
Q5: How long does it take to learn ISMS concepts?
Most beginners can understand the basic concepts within a few weeks by following a structured information systems security manager course or related training program.
Final Thoughts
Cybersecurity has become a critical priority for organizations across every industry. As digital systems continue to grow, businesses must implement structured security frameworks to protect sensitive information and maintain operational security.
Learning through an Information Security Management Course helps professionals understand how organizations identify risks, implement security controls, and manage security policies effectively. By building strong knowledge of information security management systems, learners can develop valuable skills that support careers in cybersecurity management and information security governance.